Math Topics
Learning Support
Professional
![]()


Technology Integration is a four part series on essential questions, technology integration resources, web page design, and multimedia in projects. Sections contain relevant opening essays and resources.
Part 1: Essential Questions
Part 2: Technology Integration Resources
Part 3: Web Page Design
Part 4: Multimedia in Projects
![]()
 The list of security and online safety issues continues to grow from
cyberbullying and online gangs to misuse of social networks and concerns about use
of mobile devices in school. For example, "the
widespread adoption of mobile technology has created new security
concerns. There are concerns about privacy,
access and authentication, viruses and hacking, device theft, and intellectual property
protection, as well as cheating and plagiarism. IT leaders are challenged to confront the
threats and vulnerabilities they face without merely blocking access to
valuable new apps and services" ("Mobile Tech," 2012, p. 3).
The list of security and online safety issues continues to grow from
cyberbullying and online gangs to misuse of social networks and concerns about use
of mobile devices in school. For example, "the
widespread adoption of mobile technology has created new security
concerns. There are concerns about privacy,
access and authentication, viruses and hacking, device theft, and intellectual property
protection, as well as cheating and plagiarism. IT leaders are challenged to confront the
threats and vulnerabilities they face without merely blocking access to
valuable new apps and services" ("Mobile Tech," 2012, p. 3).
Hence, keeping students safe online is essential. Nancy Willard (2009) suggested that an effective school-based strategy to address this issue of internet safety should have six components:
There should be a specific educational purpose for using the internet.
Rather than reliance on filtering, there should be better supervision and monitoring. Staff might randomly ask to view student history files for computer site access. They might expand use of technical monitoring tools (e.g., real time remote access monitoring tools or intelligent content analysis monitoring).
There should be meaningful consequences for internet misuse. However, rather than suspending privileges, which only lead to more work for teachers, students might be assigned to make a service contribution to the school or placed on "close monitoring status." This latter might be more effective with the aid of technical monitoring tools.
There should be specific steps to take for accidental access to pornography (e.g., turn off the monitor or turn it away from viewing and then report the incident).
There should be a procedure for overriding filters, which have blocked sites that really do have educational value. Selected staff might have this authority, such as library media specialists.
Classes for learning about appropriate Web 2.0 internet safety and responsible use should be developed and/or expanded for parents and students. Awareness might also be increased via workshops, school newsletters, and "just in time" postings at key places in the school, as would availability of Web 2.0 internet safety books.
The rise of using virtual worlds for learning, gaming, socializing, consumerism, and more also creates need for keeping kids safe in those environments. ConnectSafely (2010) provided Virtual World Safety Tips for Parents of Teens, which educators, students, and parents should read before becoming involved with virtual worlds. Parents should get to know their student's virtual world, their avatar, virtual friends, and so on. Students should be aware that not everyone is who they say they are. They should know to respect themselves and others in their engagements. Bullying can happen in a virtual world just as in the real world, and you should know how to combat it. All should explore safety features such as age-appropriate restricted chat, use of moderators, language filtering, tools for reporting abuse and getting help, and terms of use. Discuss password protection and not giving out passwords just to be a friend. Discuss any potential virtual consumerism available within the site. Above all students should know to exercise critical thinking in what they say, do, read, consume, upload, download, and so on.
Educators will find valuable guidelines, including in relation to the Family Educational Rights and Privacy Act (FERPA), in Protecting Student Privacy While Using Online Educational Services: Requirements and Best Practices from the Privacy Technical Assistance Center of the U.S. Department of Education (PTAC, 2014). The document addresses "privacy and security considerations relating to computer software, mobile applications (apps), and web-based tools provided by a third-party to a school or district that students and/or their parents access via the Internet and use as part of a school activity. Examples include online services that students use to access class readings, to view their learning progression, to watch video demonstrations, to comment on class activities, or to complete their homework" (pp. 1-2).
The U.S. Department of Education includes a section on Protecting Student Privacy to keep everyone up-to-date. The Department administers and enforces student privacy laws such as FERPA and the Protection of Pupil Rights Amendment (PPRA). It also provides technical assistance to help schools and school districts safeguard information about students.
HOT: Cybersecurity Awareness Program from the Department of Homeland Security "is a national public awareness campaign aimed at increasing the understanding of cyber threats and empowering the American public to be safer and more secure online" (Home page description section). The site includes multiple age-appropriate resources, particularly in its toolkit. Topics include social media, internet of things, cybersecurity while traveling, mobile device security, passwords, public WIFI, online gaming, phishing, malware, and more. There are concise tip cards for learners in grades K-8 and 9-12. You'll also find a section called Tips, which "describe and offer advice about common security issues for non-technical computer users." Below each heading within Tips are several articles that address threats, email and communication, general security information, mobile devices, privacy, safe browsing, software and applications, and more.
GoGuardian's Glossary of Technical Terms is meant to help ensure online safety. Learn about such terms as authentication, encryption, cache, cloud firewalls, content filtering, cookies, data protection, the deep web and dark web, email compression, email security, email spoofing, the internet of things security, network firewalls, remote access, spyware, and so much more.
Internet safety is so important that the Congress passed the Children's Internet Protection Act (CIPA) in December 2000 to address concerns about children's access to inappropriate internet content when using school and library computers. Although the law has been challenged in the courts, as reported by Mary Minow (2002), online safety is important for all children and particularly important for students in their early teen years who are making the transition between the greater influence of their parents to that of their peers.
Students need to understand the importance of not giving out personal information of any kind to online strangers, including their passwords and photos. They need to understand that the rules of communicating face-to-face apply online; hence, cyber-bullying is wrong, as are cheating and plagiarism. Harmful words said face-to-face hurt and the memory might fade in time; however, words stated online can stay forever. While those words might be intended only for their peers, those same words might come back to haunt the students if read by parents, teachers, college officials, potential employers, or law enforcement agents, for example.
Andrew Wallace (2013) tackled the confusion that exists among those who are required to interpret CIPA and implement it. CIPA is actually comprised of three acts: the Children's Internet Protection Act of 2000, the Neighborhood Child Internet Protection Act of 2001, and Protecting Children in the 21st Century Act of 2008, which collectively "spell out the requirements for school districts that wish to receive federal funds through the E-Rate program" (Basics section). Stating CIPA requirements in a nutshell:
School Districts must:
- Use a “technology protection measure” to block images that are: child pornography, obscene, or harmful to minors.
- Determine, with community input what content (visual or written) is inappropriate for minors.
- Adopt an Internet safety policy that applies to both students and staff.
- Teach students how interact on email, social networking sites, and in chat rooms.
- Deliver instruction with a focus on cyberbullying.
- Monitor in school use of the Internet. (Wallace, 2013, Quick Facts section)
"CIPA compliance is required for any school or library receiving E-rate funds for three of the four eligible service categories – Internet Access, Internal Connections, and Basic Maintenance of Internal Connections. Applicants for Telecommunications services only, are exempt" (E-Rate Central, n.d., Introduction to CIPA Compliance section, p. 1).
 The
COPPA Safe Harbor
Program lists companies that provide certifications that
materials are COPPA compliant. Among those are
iKeepSafe,
kidSAFE,
and TRUSTe.
The
COPPA Safe Harbor
Program lists companies that provide certifications that
materials are COPPA compliant. Among those are
iKeepSafe,
kidSAFE,
and TRUSTe.
However, per Reyes, Wijesekera, Reardon, Elazari, Razaghpanah, Vallina-Rodriguez, and Egelman (2018), be aware that such certification does not necessarily mean that the certified-app does a better job at safeguarding privacy of personal data than a non-certified app. Their study focused on Android apps available on Google Play. "Based on [their] automated analysis of 5,855 of the most popular free children’s apps, [they] found that a majority are potentially in violation of COPPA, mainly due to their use of thirdparty SDKs" (p. 63). SDK means Software Development Kit.
The National Conference of State Legislatures (2022) provides a list of State Internet Filtering Laws. "At least 27 states have Internet filtering laws that apply to publicly funded schools or libraries. The majority of these states simply require school boards/districts or public libraries to adopt Internet use policies to prevent minors from gaining access to sexually explicit, obscene or harmful materials. However, some states also require publicly funded institutions to install filtering software on library terminals or school computers." (Overview section). The summary of each state law is provided and its source.
Students and anyone who uses email or text messaging also should be cautious when opening attachments. Attachments, particularly from individuals you do not know, might contain code that is harmful to the computer itself, and enable the computer to be invaded by hackers, viruses, ransomware, and spyware.
In fact, phishing is one of the top five cybersecurity threats for schools, according to the Consortium of School Networking (CoSN, n.d.) It's a practice of sending messages that look legitimate and entice the receiver to reveal personal information or to send proprietary information, or to click on links that install malicious software. CoSN recommends "Firewalls and email systems should be configured to have rules that don’t allow bad attachments" (p. 1). Phishing is not always easy to detect. Google has a quiz to see how well you can spot phishing.
In its findings, the National Center for Education Statistics reported that nearly all U.S. public schools in 2005 with Internet access used various technologies or procedures to control student access to inappropriate content. Leading the approaches were blocking and filtering software (99%), teachers or other staff monitored Internet access (96%), parents signed written contracts (79%), students signed written contracts (76%), monitoring software (67%), honor codes (53%), and school restrictions to its own intranet (46%). Leading methods to inform students and parents about approaches included via school policies or rules, newsletters, messages posted on the school web site, school bulletin boards, and pop-up messages when students log-on to computers or the Internet (Wells & Lewis, 2006).
Filtering enables you to control what sites users can or cannot access based on pre-determined criteria set at the administrator's level. Schools can prevent students from accessing sites with sexual, violent, gambling, and non-educational themes. But with so many sites out there, setting the filtering criteria so that relevant sites are not blocked and then maintaining the Web filter's site database can be a challenge. An ability to authenticate users and identify their activities on a network can be an important accountability feature, particularly for students who try to access blocked sites (Careless, 2007). Althouigh students might know how to circumvent content-filters, Willard (2009) noted that students do not always have evil intentions when trying to access blocked sites. They might be just trying to access their social networking sites, which schools have been known to block.
Web filters can be software or hardware based and those of high value to schools are not necessarily cheap. A sophisticated feature to look for is one that "constantly records and rates new Web sites as they appear, then sends this data to your Web filter to keep it up to date" (Careless, 2007, p. 10). However, there are free web-filtering services. OpenDNS (DNS stands for Domain Name System) provides content filtering, phishing protection, domain blocking, adult site blocking, web proxy blocking, and a domain whitelisting feature. This latter gives the user final say in what is blocked. There's no hardware to buy, or software to install.
WebPurify provides tools for photo and video moderation and a profanity filter for user generated content (UGC). Photos and videos, including the audio, can be examined and then rejected for inappropriate content such as nudity, hate or hate crimes, violence, offensive gestures, drug related activities, and blank or broken images, or your custom criteria. The profanity filter allows you to manage your own block and allow lists. It also includes an email, phone, and URL filter. The site's blog contains multiple useful articles and guides on UGC. UGC can be shared on websites, social media platforms, marketing channels to promote their brands or services, blogs, podcasts, and so on, making WebPurify a useful platform to consider for a proactive approach to computer and online safety. Each tool is not free, but includes a free trial.
If access control and filtering are concerns to help keep kids safe online, consider making a list of the controls you would need when searching for an Internet service provider (ISP), and check if those parental controls are available with the plan you are considering. Look for directions from the ISP to help configure kid-safe internet filtering. For example, see directions from Frontier, Verizon, and Xfinity.
Parents and students need access to a school acceptable use policy (AUP) for technology. An effective AUP addresses two goals: "shielding students from harmful material and enabling access to beneficial internet resources" (Pierce, 2012, online p. 2).
Overall, there is no single blueprint for creating AUPs, but organizations such as Common Sense Media have developed guidelines and samples, and gathered numerous resources to assist developers. In its 1-to-1 Essentials program, Common Sense Media provided the following topics that developers may want to address:
The AUP policy should address technology devices that learners bring to school, which is commonly referred to as BYOD. J. Robinson (2013) noted that a clear definition of such devices, users, violations, and consequences to violations should be included in the AUP, as well as disclaimers.
The BYOD policy at Newton-Conover City Schools in North Carolina includes any devices and accompanying media (e.g., USB thumb and external hard drives) capable of connecting to their wireless network. BYOD users include not just students, but anyone (employees and guests) who can connect to the wireless network.
A BYOD policy should make it clear that the purpose of the wireless infrastructure is to support instruction. The policy should define when devices become a disruption and spell out offenses resulting in loss of wireless connectivity privileges. At Newton-Conover these latter include accessing web sites of a pornographic nature or with illegal content; cyber-bullying or harassment of other users, and engaging in activities of a malicious or illegal intent. The BYOD policy should include disclaimers, such as the district not being responsible for providing tech support for personal devices, and not being responsible for damage, theft, or loss of personal devices. J. Robinson (2013) also recommended that districts review and update their BYOD policy and procedures as least once a year.
Policies should address cellphone use and when you can search a student's phone, a topic explored by Ariel Fox Johnson, Senior Counsel for Policy and Privacy at Common Sense Media (2018). Because policies and practices vary among educators, schools, districts, and states, guidelines on legal searches and examples of the same are needed for administrators, teachers, students, and parents to provide clarity. Per Johnson:
"While the Supreme Court held in 2014 that police need a warrant to search a cellphone, schools have historically had a little more leeway with searches, be they bags, lockers or, these days, devices. Typically, if a student, parent or teacher challenges a search, courts will consider whether the search was justified at its inception — it was reasonable to think the search would turn up evidence the student was violating rules or laws — and whether the search’s scope was reasonably related to the circumstances that led to the search in the first place." (Johnson, 2018, para. 4)
In considering updating existing policies, Nancy Caramanico (2011) suggested to address Web 2.0 (including student online posts and how they will be monitored by teachers), cellphone use (including texting and under what circumstances), devices that enable portable internet hot spots (e.g, MiFis), other mobile devices (e.g., laptops, rules for usage, who owns them, insurance), social media and social networks and rules for their use, taking digital images (permissions needed, including use of student names), and outside of school use of technology.
Note: There is a movement to ban or limit cellphone use in schools, which might also include smartwatches. For example, in its article, State policies on cellphone use in K-12 public schools, Ballotpedia (n.d.) noted "As of April 6, 2026, 41 states had enacted laws or policies on K-12 classroom or school cellphone usage." You'll also find a map of the U.S. where you can find the status of the policy in your state.
So whether you are developing a new AUP or revising an existing policy, Sylvia Martinez (2020) provided a perspective to consider. An AUP "should include the benefits of using ed tech -- not just promises of punishment (para. 1). Her guiding questions to serve in a review or development process include:
Consider rethinking your AUP in terms of a Responsible Use Agreement (RUA).
In its 2026 resource Setting Conditions for Success: Guidelines for Responsible Use of Technology for Schools,The Consortium for School Networking (CoSN) provided guidance "intended to complement—not replace—district policies governing the use of technology and digital resources" (p. 1). CoSN noted "While AUPs serve an important purpose, they are often written in formal or legal language that can be difficult for students and families to understand and act on." CoSN encourages school systems to adopt Responsible Use Agreements (RUAs), as they take "a more student- and family-friendly approach that prioritizes clarity, accessibility, and the development of a healthy digital culture both at school and at home" (pp. 2-3). They are written in plain English, emphasizing the do's of technology use rather than the don'ts, and engage the whole school community for their input. Further, the RUA includes statements of what to do if something goes wrong, and consequences of misuse. The RUA templates for elementary and secondary schools included in this publication are of particular value, each of which can be edited to meet a district's goals and culture.
![]() Address
artificial Intelligence (AI) use in your AUP: With the rise of AI and its impact on learning, the school's AUP policy should
also be updated to address acceptable uses of applications that employ AI. Steve
Baule (2024) provided
5 Key AI Policy Considerations:
Address
artificial Intelligence (AI) use in your AUP: With the rise of AI and its impact on learning, the school's AUP policy should
also be updated to address acceptable uses of applications that employ AI. Steve
Baule (2024) provided
5 Key AI Policy Considerations:
HOT!: AI for Education contains State AI Guidance for K12 Schools. This resource includes summaries and links to the full guidance or policy on the use of AI in K12 schools from 33 states and Puerto Rico as of October 28, 2025. The site also includes additional AI resources.
HOT!: TeachAI has an AI Guidance for Schools Toolkit. It contains Sample Guidance on the Use of AI and Sample Considerations for Existing Policies to help in writing addendums to existing policies. Its section on Principles of AI in Education contains examples of AI statements and AI initiatives from schools around the country. There is also a Sample Student Agreement on the Use of AI and sample language for a classroom policy of the use of AI that educators might consider for an addition to a syllabus.
In their Review of Guidance from Seven States on AI in Education, Jeremy Roschelle, Judi Fusco, and Pati Ruiz (2024) reviewed guidance documents from California, North Carolina, Ohio, Oregon, Virginia, Washington state, and West Virginia on how to approach artificial intelligence in education. The report published by Digital Promise includes major common themes, opportunities to use AI, risks of using AI, and key points on what school districts should do with regard to policy development. As to this latter, the authors also included that new AI policies "must be aligned with regulations, such as FERPA, COPPA, IDEA, and CIPA, to ensure compliance with data privacy and security laws" (p. 8). Also see Digital Promise's initiative on Artificial Intelligence in Education for additional resources. Note: The Ohio Department of Education and Workforce (2025), informed by the work of the Ohio AI in Education Coalition, has developed a model AI policy that schools may choose to adopt.
The AUP should require full disclosure statements regarding content created with AI tools, applicable for both students and staff. For example, in its Sample Guidance on Staff Use of Generative AI for K-12 School Districts, Michigan Virtual (2024) recommended that staff provide full disclosure "Whenever AI tools contribute to the development of higher profile educational materials, research, or work-related artifacts, or are being used to record/summarize others’ contributions. (eg. "AI assisted X District staff in the creation of this resource," OR "X% of this document was created with AI.")" (Disclosure section).
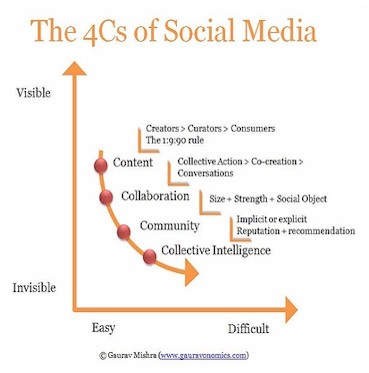
To address social media, policy developers need to first define social media, as the term does not mean the same to all. Taking a tools perspective can be overwhelming. As Gaurav Mishra (2009) noted, "social media encompasses many different types of tools, and each tool has specific characteristics and a steep learning curve" (para. 2). Differences can been seen in social media tools such as "Blogging (WordPress), microblogging (Twitter*), video-sharing (YouTube), photo-sharing (Flickr), podcasting (Blog Talk Radio), mapping (Google Maps), social networking (Facebook), social voting (Digg), social bookmarking (Delicious), lifestreaming (Friendfeed), wikis (Wikipedia), and virtual worlds (Second Life)" (para. 2). (*As of July 2023 Twitter is now known as X.)
As tools come and go, policy makers can better justify their inclusion in the learning environment, if social media is viewed as tools and practices that focus on the 4C's: content, collaboration, community, and collective intelligence. Per Mishra (2009), these constitute its value system:
In fact, Meris Stansbury (2017) indicated educators have alternatives to social media platforms such as Facebook and Twitter*, which can be distractors for teaching and learning and which also can create problems with privacy, security, and online bullying. Educators can "use a classroom or subject-specific forum or platform" for collaboration and discussions. There are also apps for team collaborations, such as Slack for iOS or Slack for Android. (*As of July 2023 Twitter is now known as X.)
Educators are exploring ways to use mobile technologies in learning. As in higher education, we need mobile learning strategies at K-12 that support academic plans "emphasizing experiential learning, interdisciplinary research, creative expression, urban engagement and global opportunity" ("Mobile Tech", 2012, p. 2). According to the Consortium for School Networking (CoSN) and the FrameWorks Institute (2012), "Before steps are taken to impose limits on the use of social media and mobile technologies in schools, policymakers and educators need to consider the consequences for learning that such restrictions would produce" (p. 2). Further, "One of the most powerful reasons to permit the use of social media and mobile devices in the classroom is to provide an opportunity for students to learn about their use in a supervised environment that emphasizes the development of attitudes and skills that will help keep them safe outside of school" (p. 2).
As a starting point for discussions on responsible use in a supervised environment, educators might consider the information in the Women's Guide to Cyber Safety 2022 by Sarah Frazier (2022). The tips on harassment (e.g., online dating, online gaming, workplace), use of Facebook, Twitter*, Snapchat, Tiktok, sharing photos, using online forums and messaging apps, preventing and stopping hacking and doxxing, and so on are not just for women, as anyone will benefit. The tips also give insights into development of an AUP. (*Note: As of July 2023 Twitter is now known as X.)
If one views a social media definition in terms of Mishra's 4C's (2009), then banning social media as a general policy is no longer an issue. Likewise, banning mobile technologies in general is not the answer for ensuring safety. Mobile devices have become an integral part of society and students' lives. Hence, as James Bosco (2013) noted, there are districts that "have altered the perspective on acceptable” use policies by framing them as “responsible” use policies. A “responsible use” approach is more than just a switch in terminology. It presents the student use policy in the form of what students should do rather than what they should not do" (p. 7).
For further reading and examples of AUPs, consider the following:
Heartland Community Schools (NE) Laptop Policy, Procedures, and Information Handbook.
Lake Washington School District (WA) Student Acceptable Use Procedures AUP.
Science Leadership Academy (PA) Acceptable Use Policy applies to "to any electronic device including laptops, mobile phones, MP3 players, gaming devices, digital cameras, any and all devices that are connected to the School District of Philadelphia network" (SLA Blog post, 2012, November 19, para. 2).
Len Scrogan (2007) provided help in his AUPs in a Web 2.0 World.
CoSN (Bosco, 2013) published an updated Rethinking Acceptable Use Policies to Enable Digital Learning: A Guide for School Districts.
Information Security in Education/Security Policies for Mobile Devices is posted in Wikibooks. It contains benefits and risks of mobile devices in education, consequences of misuse, writing acceptable use policies that address mobile devices, sample AUPs, and additional resources.
Acceptable Use Policies that Focus on Student Learning (2014) contains a list of resources about updating AUPs and sample school district policies brought to you by K12blueprint.com.
New York City Department of Education resources include its Internet acceptable use policy. Its Digital Citizenship resources include Social Media Guidelines in two parts--those for students 12 and under, and for students over 13. Comparable guides at each level are available for parents.

Get a promise from students to be LARK, and when they cross the line, ask them if what they did is LARK, that is Legal, Appropriate, Responsible, and Kind. It’s an acronym they most likely will remember, suggested by Pamela Livingston (2007, August 2) in her Classroom 2.0 blog post on AUPs. The term has no copyright.
If so, in addition to an Acceptable Use Policy, you should have a mobile device loan agreement for students. The following resources provide ideas for such content.
ConnectSafely.org produced A Parents' Guide to Mobile Phones. It includes some good information on how kids use mobile phones, your child's first mobile phone, tips on use and keeping them safe when using such devices, and parental controls. Classroom teachers will also benefit from this information.
Jamie Nunez and Christine Elgersma (2024) addressed A Community-First Approach to Cellphone Bans, posted at Common Sense Education. To decide to fully ban, partially ban, or not ban at all, they provided the following tips, and several resources related to their tips:
HOT! The U.S. Department of Education, Office of Educational Technology (2024) developed A Playbook for Student Personal Device Policies "which provides one approach to collaboration as you work to determine the best implementation plan for establishing any research-based cellphone policy. The Playbook can help education officials to engage community members in developing clear, consistent, and research-informed policies." (p. 6).
See the following app:
 Bark
for iPhone and Android
"helps families manage and protect their children’s online lives. [It
can] monitor 30+ of the most popular apps and social media platforms,
including text messaging and email, for signs of digital dangers. [Its]
screen time management and web filtering tools help you set healthy limits
around how and when your kids use their devices." (Site description)
Bark
for iPhone and Android
"helps families manage and protect their children’s online lives. [It
can] monitor 30+ of the most popular apps and social media platforms,
including text messaging and email, for signs of digital dangers. [Its]
screen time management and web filtering tools help you set healthy limits
around how and when your kids use their devices." (Site description)
Note: YouTube is a very popular site. You can protect youth against access to inappropriate content using YouTube's "Restricted Mode." Search for this latter phrase on YouTube to learn how, or view Alan Spicer's short video: How To Turn On / Off Restricted Mode in NEW YouTube Studio.
See the following app:
 Qustodio allows you to
supervise your kids online. Control access to pornography, filter
harmful websites, monitor calls, SMS, web activities, set time limits to
manage online experiences, including social networking, each day without the
drama; set time limits for games and apps. You can even track your
child's location. K-12 Schools can also benefit from this app for
online safety, device management, and usage supervision.
Qustodio allows you to
supervise your kids online. Control access to pornography, filter
harmful websites, monitor calls, SMS, web activities, set time limits to
manage online experiences, including social networking, each day without the
drama; set time limits for games and apps. You can even track your
child's location. K-12 Schools can also benefit from this app for
online safety, device management, and usage supervision.
Parents should also be aware of the Protection of Pupil Rights Amendment (PPRA), which "is intended to protect the rights of parents and students in two ways. The first is by seeking to ensure that schools and contractors make instructional materials available for parents’ inspection if those materials will be used in connection with a survey, analysis, or evaluation funded by the U.S. Department of Education. Second, PPRA requires that a school district, with exceptions, directly notify parents of students who are scheduled to participate in activities involving the collection, disclosure, or use of personal information collected from the students for marketing purposes or for sale or provision to others for marketing purposes and give parents the opportunity to opt out of these activities. One important exception to PPRA is that neither parental notice and the opportunity to opt out nor the development and adoption of policies are required for school districts to use students’ personal information for the exclusive purpose of developing, evaluating, or providing educational products or services for students or schools" (U.S. Department of Education, Office of Educational Technology, 2014, pp. 60-61).
Parents, you might wish to check the social media apps that your children are using. Some that are popular with teens are dangerous. Read Social Media and Teens: The Ultimate Guide to Keeping Kids Safe Online (2018) posted at Educate Empower Kids. It also includes a Social Media Contract and helpful guidelines for parents.
Caution: Before selecting an app or tool that uses AI, educators and parents should examine the AI Risk Assessments, noted by Common Sense Media.
For example, in its review of ChatGPT-5, Common Sense Media rated its risk factor as "high." Although, "it can be valuable for learning, creativity, and homework support, particularly with Study Mode" there are significant concerns "around teens using ChatGPT for emotional support and mental health advice. Common Sense Media research shows this usage is both popular among teens and developmentally inappropriate." The technology "doesn't respond like an adult would, doesn't always detect when a teen is at risk, and becomes less safe during extended conversations."
NOTE: Look for digital citizenship resources that address artificial intelligence. In its Framework for Implementing Artificial Intelligence (AI) in K-12 Education, the ILO Group (2024) recommended revising your digital literacy curriculum to account for AI, stating the following:
"Update your students' digital literacy curriculum by focusing on understanding and interacting responsibly with AI technologies. Material may include:
- Basics of AI: Introduce students to the principles of AI, including machine learning and natural language processing.
- Ethical AI Use: Teach about the ethical implications of AI, including privacy concerns and bias in AI algorithms.
- Safe Online Behaviors: Include basic information on how students can protect their personal data and practice safe online behaviors." (ILO Group, 2024, p. 9)
HOT! Be Internet Awesome from Google includes a curriculum (lesson plans and classroom activities) and four challenging games in the Interland that teach learners to be responsible and safe online. It received a seal of approval by the International Society for Technology in Education (ISTE) for its pedagogic value and alignment to ISTE standards.
BrainPOP.com includes a free movie: Digital Etiquette. A quiz and lesson idea are also provided.
Childnet (London, UK) includes numerous resources on topics such as social media, digital well being, online bullying, sexting, parental controls, screen time, and so on. You can search by age range, topic, and type of resource (e.g, video, lesson plan, presentation, toolkit, etc).
Common Sense Media has multiple programs. For example:
Connect Safely is for parents, teens, educators, advocates - everyone engaged in and interested in the impact of the social Web. Of high relevance are the parent guides, which help users to understand topics such as TikTok, online hate speech, Roblox, Instagram, Cyberbullying, Saturn, Cybersecurity, Educational Technology, Mobile Phones, and more.
Consortium for School Networking (CoSN) maintains a section of its website devoted to EdTech topics, such as Cybersecurity, Driving K-12 Innovation, Interoperability, and Artificial Intelligence. At CoSN you can also download the Protecting Privacy in Connected Learning Toolkit, a "step-by-step guide to navigating the complexity of the Family Education Rights and Privacy Act (FERPA) and Children’s Online Privacy Protection Act (COPPA) and related privacy issues. The toolkit is organized in the form of a decision tree, or flowchart, and addresses FERPA and COPPA compliance issues as well as smart suggested practices that reach beyond compliance. Also included in the toolkit are definitions, checklists, examples, and key questions to ask." Also see CoSN's U.S. State of Ed Tech 2026, which "examines both emerging and long-standing issues, including artificial intelligence, cybersecurity, connectivity, staffing, procurement, and device management" (p. 2). Education leaders ranked cybersecurity at their #1 priority, followed by data privacy and security, gen AI, cost-effective/smart budgeting, and network infrastructure (p. 19). Top challenges to technology implementation included budget constraints and lack of resources, existence of silos in the district, which make it difficult to work together on technology planning, and unavailable relevant training and professional development (p. 20).
CYBER.ORG addresses cybersecurity. It provides free professionial development, curricula, and resources for educators who wish to integrate cybersecurity lessons and courses into their classrooms. Subjects addressed include Career & Technical Education, Cybersecurity, Engineering, Humanities, Robotics & Coding, Math, Science, and Computer Science. Content is aligned to learning standards. Cyber.org developed K-12 Cybersecurity Learning Standards (2021), which are presented within grade bands K-2, 3-5, 6-8, and 9-12 and address three themes: computing systems, digital citizenship, and security.
 Cyberbullying Research Center "is
dedicated to providing up-to-date information about the nature, extent,
causes, and consequences of cyberbullying among adolescents. ... [It] serves
as a clearinghouse of information concerning the
ways adolescents use and misuse technology. It is intended to be a
resource for parents, educators, law enforcement officers, counselors,
and others who work with youth. Here you will find facts, figures, and
detailed stories from those who have been directly impacted by online
aggression. In addition, the site includes numerous resources to help
you prevent and respond to cyberbullying incidents" (About Us section).
See Bullying Laws Across
America.
Cyberbullying Research Center "is
dedicated to providing up-to-date information about the nature, extent,
causes, and consequences of cyberbullying among adolescents. ... [It] serves
as a clearinghouse of information concerning the
ways adolescents use and misuse technology. It is intended to be a
resource for parents, educators, law enforcement officers, counselors,
and others who work with youth. Here you will find facts, figures, and
detailed stories from those who have been directly impacted by online
aggression. In addition, the site includes numerous resources to help
you prevent and respond to cyberbullying incidents" (About Us section).
See Bullying Laws Across
America.
Cybersecurity Awareness for College Students: 7 Things to Do Now from Purdue University Global (2020) elaborates on the following tips, which are also helpful for all:
 Digital Citizenship: Using Technology Appropriately:
The site includes nine themes of digital citizenship and provides resources and
publications on this theme. The nine themes, developed by Mike Ribble,
pertain to digital access, commerce, communication and collaboration, etiquette,
fluency, health and welfare, law, rights and responsibilities, and security and
privacy. The site also includes a
digital citizenship progressions chart,
which shows appropriate introduction of elements of each theme to students by
grade level bands. Ribble and Marty Park are the authors of
The Digital Citizenship Handbook for School Leaders: Fostering Positive Interactions Online
(2019).
Digital Citizenship: Using Technology Appropriately:
The site includes nine themes of digital citizenship and provides resources and
publications on this theme. The nine themes, developed by Mike Ribble,
pertain to digital access, commerce, communication and collaboration, etiquette,
fluency, health and welfare, law, rights and responsibilities, and security and
privacy. The site also includes a
digital citizenship progressions chart,
which shows appropriate introduction of elements of each theme to students by
grade level bands. Ribble and Marty Park are the authors of
The Digital Citizenship Handbook for School Leaders: Fostering Positive Interactions Online
(2019).
HOT! The Digital Citizenship+ (Plus) Resource Platform (DCPR) is "an evolving collection of learning experiences, visualizations, and other educational resources (collectively referred to as “tools”)" designed to help you learn about different areas of youth’s (ages 11-18) digitally connected life. Seventeen sections are available with "tools across digital life." They include Artificial Intelligence, Civic and Political Engagement, Computational Thinking, Content Production, Context, Data, Digital Access, Digital Economy, Digital (Literacy), Identity Exploration and Formation, Information Quality, Law, Media (Literacy), Positive/Respectful Behavior, Privacy and Reputation, Safety and Well-being, and Security (About section). There is a well-developed curriculum with resources that can be used in and out of classroooms. The tool type, media format, and target age are indicated in each activity.
EverFI's Ignition: Digital Wellness and Safety is a digital literacy curriculum for grades 6-9, which includes six lessons based on ISTE standards for students. Lesson 1 delves into connections and community; lesson 2 addresses safety and privacy; lesson 3 is on screen-time and offline time; lesson 4 is on technology and data; lesson 5 includes rights and literacy; and lesson 6 is on evaluating content.
Family Online Safety Institute has resources for good digital parenting, and a section for policy and research. You can search by age ranges, category, and digital type.
A Guide to Internet Safety: How to Keep Kids and Teens Safe Online was written by Ray Walsh (2020) of the UK. You'll find relevant information for on the importance of internet safety, what online dangers exist, online privacy, the good and bad of the modern internet, house rules for the computer, antivirus software, child-friendly search engines, parental controls, information for teens, mobile device safety, social networks, and more. The guide includes related content resources.
![]() How to Keep your Children Safe Online: The Ultimate Guide for the non
Techy Parent by Chris Hauk (2023) at Pixel Privacy is a comprehensive guide to
internet safety for non-techy parents/carers. It covers the dangers of the
internet, suggestions for rules and how to use parental controls (e.g., those
available on Windows, MacOS, iOS, and Android platforms, and for videos on
iTunes and YouTube). Additional
Online Privacy Guides are
available in Resources.
How to Keep your Children Safe Online: The Ultimate Guide for the non
Techy Parent by Chris Hauk (2023) at Pixel Privacy is a comprehensive guide to
internet safety for non-techy parents/carers. It covers the dangers of the
internet, suggestions for rules and how to use parental controls (e.g., those
available on Windows, MacOS, iOS, and Android platforms, and for videos on
iTunes and YouTube). Additional
Online Privacy Guides are
available in Resources.
Identity Theft and Online Security from the Federal Trade Commission provides sections on how to protect your personal information and privacy, and f kids online. You'll find advice on topics such as securing your devices, malware, scams, VPNs, passwords, social networking, sexting, cyberbullying, communicating online and phishing, appropriate use of mobile phones and texting, virtual worlds, parental controls, and more. Also of value is Net Cetera: Chatting with Kids About Being Online, which offers practical advice and ideas for parents, teachers,and others to get a conversation started about social networking, privacy, mobile devices, computer security, and dealing with cyberbullying.
International Society for Technology in Education (ISTE) Digital Citizenship Lessons are provided for elementary, middle, and high school learners. These free lessons address digital competencies resulting from the impact of AI, as noted in the updated ISTE standards of 2024.
HOT! Internet Matters will help parents and teachers to keep children safe online. You'll find sections on online issues (e.g., cyberbullying, sexting, self-harm, screen time, radicalization, online reputation, inappropriate content, and more), age-specific advice and checklists, setting safety controls on a range of devices, guides and resources, and resources for schools, and a news and expert opinion section.
K12 Security Information eXchange (K12 SIX) " is a nonprofit threat intelligence and best practices sharing community for members of the U.S. K-12 education community committed to preventing and responding to cyber threats, together." Annual membership fees are based on student enrollment.
LearnFree: Internet Safety includes a series of tutorials on several topics, such as creating strong passwords, browser security, spam and phishing, malware, safe online shopping, browser tracking, social media privacy, what to do if you get a computer virus, browser plug-ins, using phone verification, wi-fi security, and driving safely while using mobile devices. There's a quiz on internet safety. Teacher guides are provided.
MediaSmarts from Canada promotes digital and media literacy through its programs and resources for homes, schools, and communities. There are numerous teacher resources.
![]() NetSmartz is an educational safety resource
from the National Center for Missing & Exploited Children® and Boys &
Girls Clubs of America for children (ages 5-17), parents, guardians,
educators, and law enforcement. Teach children how to stay
safer on the Internet with this resource.
NetSmartz is an educational safety resource
from the National Center for Missing & Exploited Children® and Boys &
Girls Clubs of America for children (ages 5-17), parents, guardians,
educators, and law enforcement. Teach children how to stay
safer on the Internet with this resource.
Online Safety for Children and Teens: A Comprehensive Guide to Staying Safe Online from cyberinsureone.com includes several sections with associated additional resources on dangers that children can encounter online, and specific sections devoted to the basics of online safety for children, tweens, and teens, and digital citizenship.
Our Space is a set of free "curricular materials designed to encourage high school students to reflect on the ethical dimensions of their participation in new media environments. Through role-playing activities and reflective exercises, students are asked to consider the ethical responsibilities of other people, and whether and how they behave ethically themselves online. These issues are raised in relation to five core themes that are highly relevant online: identity, privacy, authorship and ownership, credibility, and participation." These materials were developed via a collaboration of the GoodPlay Project of Harvard Graduate School of Education and Project New Media Literacies of the University of Southern California.
HOT: Pacer's National Bullying Prevention Center: Cyberbullying defines cyberbullying, offers ways to help youth, includes an FAQ section, statistics and facts, and ends with a short quick to test your knowledge on this topic. Informative videos are included. Elementary and middle/high school educators will also find a curriculum and activies to address bullying in general. There are also parent resources.
Parents: Bullying A search for "bullying" at Parents.com reveals numerous articles on bullying, including cyberbullying. Learn about the different types, where it happens, and how to respond.
PBS Learning Media Digital Citizenship resources address multiple topics: Safe, Legal, and Responsible Use; Digital Access, Digital Commerce, Digital Health and Wellness; Digital Literacy, Digital Communication, Collaborative and Positive Attitude, Lifelong Learning, Leadership, and Ethical Use and Impact.
PBS NOVA Labs include the free game-based Cybersecurity Lab designed for grades 6-12 "in which players will discover how they can keep their digital lives safe and develop an understanding of cyber threats and defenses. Players will advance by using computer coding, logical reasoning, critical thinking, and vulnerability detection to solve various problems. These are the same skills employed regularly by cybersecurity professionals. However, players won’t need any prior cybersecurity or coding expertise to succeed" (About section). An educator guide is provided. Also see the Cybersecurity videos.
HOT: Planet Nutshell: NetSafe is a series of 18 video episodes on internet safety presented in an engaging cartoon format. Episodes 1-14 are designed for learners in K-12; episodes 15-18 delve into tips and tools for parents, mobile devices in distracted driving, use of public wi-fi, and mobile location privacy. You can also download transcripts.
Stay Safe Online, sponsored by the National Cyber Security Alliance, contains the information you need to secure your home or small business computer. You'll find tips on how to safeguard your system (e.g., disconnect from the Internet when not in use), a self-guided cyber security test, beginner's guides to online security, and other Internet security resources.
StopBullying.gov provides "information from various government agencies on how kids, teens, young adults, parents, educators and others in the community can prevent or stop bullying" (About Us section). Cyberbullying is also addressed.
The Ultimate Guide to Protecting Children Online in 2022 by Jack Foster (2022) includes tips and techniques on Restricting YouTube, Social Media Privacy, Anti-viruses, Virtual Private Networks, Game Consoles, Unwanted Messages, setting Parental Controls.
WebWiseKids contains "resources to equip young people to safely use and enjoy the latest technologies." For example, students can learn how to safely engage in social networks. There's a game using real life stories to learn how to safely use a cellphone. There are classroom resources on internet safety that can be used with students, even those in kindergarten.
 Data
breaches, denial of service, spoofing/phishing, malware/scareware (including
ransomware), unpatched or outdated software vulnerabilities, and
removable media are among threats facing school and school district
networks and systems (Readiness and Emergency Management for Schools
Technical Assistance Center, n.d., pp. 2-3). Avoiding problems
requires monitoring networks continually, policies on acceptable use,
storing data securely, and creating firewalls and lists of approved
individuals who can access the school or district's networks and systems
(p. 3).
Data
breaches, denial of service, spoofing/phishing, malware/scareware (including
ransomware), unpatched or outdated software vulnerabilities, and
removable media are among threats facing school and school district
networks and systems (Readiness and Emergency Management for Schools
Technical Assistance Center, n.d., pp. 2-3). Avoiding problems
requires monitoring networks continually, policies on acceptable use,
storing data securely, and creating firewalls and lists of approved
individuals who can access the school or district's networks and systems
(p. 3).
The K-12 Cybersecurity Resource Center has a 20-minute, 50-question cybersecurity self-assessment tool--see its Essentials Series. Per its description it is "intended to help school districts to identify and prioritize cybersecurity controls. This assessment is based on the NIST Cybersecurity Framework, adapted for U.S. K-12 school districts and focused on practical, relevant examples. Completing the questionnaire will generate a printable-report with customized, detailed feedback. The report can be used to communicate priorities to district leadership, as well as to help provide a roadmap for school district IT leaders seeking to shore up their district's cybersecurity controls." The NIST is the National Institute of Standards and Technology.
Districts would also benefit from the Cybersecurity Rubric (2023, March), a free self-assessment tool for schools from cybersecurityrubric.org. You can evaluate where your practices fall on a scale of 1 to 5, that is from initial to optimized. The framework has five functions (identify, protect, detect, respond, recover) and 23 categories. Free training to use the rubric is available at no cost and takes about 2.5 hours to complete.
The K-12 Cybersecurity Resource Center has maintained an interactive map of cyber-incidents as reported about U.S. K-12 public schools and districts since 2016. The map identifies where the incident occurred and type of breach. There's also a District LookUp feature to check if your incident is listed. The site provides additional cybersecurity resources.
K-12 districts should be aware of the K-12 Cybersecurity Act of 2021, signed into law by President Joe Biden on October 8, 2021. The ultimate goal of the law was development of recommendations for cybersecurity guidelines for K-12 schools, based on a study of specific risks impacting K-12 institutions (Nagel, 2021). See the text of the law, Senate Bill: 1917. The study was conducted by the Cybersecurity and Infrastructure Security Agency (CISA), which is part of of the Department of Homeland Security in the U.S. government. In January 2023, CISA published its report, Protecting Our Future: Partnering to Safeguard K-12 Organizations from Cybersecurity Threats. The report is accompanied by "three one-sheet reference guides on key findings, recommendations, and the most impactful security measures."
Schools and school districts will benefit from additional information contained within the following:
In The Ultimate Online Privacy Guide (2022), Jack Foster (2022) elaborated on the following tips for ensuring online privacy and protecting your devices:
ConnectSafely "is a Silicon Valley, California-based nonprofit organization dedicated to educating users of connected technology about safety, privacy and security. Here you’ll find research-based safety tips, parents’ guidebooks, advice, news and commentary on all aspects of tech use and policy" (About Us section). Highly recommended. The site also includes a media library with videos, talks, and presentations.
ConsumerAffairs.com includes reviews for 10 best rated antivirus software companies. At the top of the list are Total Defense, MyCleanPC.com, and Webroot AntiVirus.
Gaggle provides safe online learning tools specifically created for K-12: email, a human monitoring service, GaggleTube (for safe videos), web hosting and design, assignment drop boxes, blogs, instant messaging, digital lockers, class pages, calendar, safe texting, markup for feedback on assignments, discussion boards, social learning, mobile apps. "Gaggle features built-in processes and classroom workflows designed to promote educator and student productivity. Teachers can easily create, assign, collect and correct assignments on their schedule, while promoting student engagement and embracing the benefits of social networking in a safe and controlled environment" (Overview section). Among resources is a Content Library. A Buyer's Guide: Teaching and Learning Platform Safety Checklist (2013, October) contained the following key safety criteria for selecting the safest platform for your school:
GoGuardian "provides device management solutions that keep students safer online and make teaching easier." You'll find a parent app and solutions for classroom management, filtering and monitoring, asset tracking, engagement analytics, suicide prevention, and more.
KeePass is "a free open source password manager, which helps you to manage your passwords in a secure way. You can put all your passwords in one database, which is locked with one master key or a key file. So you only have to remember one single master password or select the key file to unlock the whole database. The databases are encrypted" for security (What is KeePass? section).
How Firewalls Work by Jeff Tyson, posted at HowStuffWorks.
 In
Free and Low Cost Software to Make Computing Easier
Miquel Guhlin (2005), a Texas school district instructional technology services
director, suggests software and provides advice on compressing multiple
files for transfer as an email attachment, setting up your own Web server,
FTP server, and Email (SMTP) server; protection from
spyware/adware/viruses; and selecting alternative browsers to Internet
Explorer; and ensuring that your email is private, not public.
In
Free and Low Cost Software to Make Computing Easier
Miquel Guhlin (2005), a Texas school district instructional technology services
director, suggests software and provides advice on compressing multiple
files for transfer as an email attachment, setting up your own Web server,
FTP server, and Email (SMTP) server; protection from
spyware/adware/viruses; and selecting alternative browsers to Internet
Explorer; and ensuring that your email is private, not public.
Free software is on sites such as SourceForge and CNET's Download. Other software recommendations include Zone Alarm firewall, AVG antivirus, Avast free antivirus for your PC, Avira free antivirus, and Bitdefender antivirus free edition.
PasswordManager.com includes a list of the best password managers for a variety of devices, including password managers that are free. You'll also find reviews, comparisons and other help for selecting the most appropriate for your devices.
Back to top | Part 2: Technology Integration Resources: Page 1 | 2 | 3 | 4
Ballotpedia. (n.d.). State policies on cellphone use in K-12 public schools. https://ballotpedia.org/State_policies_on_cellphone_use_in_K-12_public_schools
Baule, S. (2024, January 8). 5 key policy considerations for regulating AI in classrooms. Tech & Learning. https://www.techlearning.com/news/5-key-policy-considerations-for-regulating-ai-in-classrooms
Bosco, J. (2013). Rethinking acceptable use policies in to enable digital learning: A guide for school districts. Washington, DC: Consortium for School Networking. https://practices.learningaccelerator.org/artifacts/cosn-rethinking-acceptable-use-policies-to-enable-digital-learning-a-guide-for-school-districts
Caramanico, N. (2011). Brush up your AUP. Tech & Learning, 31(11), 52-54. https://www.techlearning.com/news/brush-up-your-aup
Careless, J. (2007, April). The filtering challenge. Technology & Learning, 27(9), 8-10. https://www.techlearning.com/news/the-filtering-challenge
ConnectSafely. (2010, January 8). Virtual world safety tips for parents of teens. http://web.archive.org/web/20220320003950/https://www.connectsafely.org/pdfs/tips_vw_teens_01_2010.pdf
Consortium for School Networking. (n.d.). Top 5 cybersecurity threats for schools. https://www.cosn.org/wp-content/uploads/2022/01/Top-5-Cybersecurity-Threats.pdf
Consortium for School Networkinig. (2026). Setting conditions for success: Guidelines for responsible use of technology for schools. https://www.cosn.org/wp-content/uploads/2026/04/Setting-Conditions-for-Success-2026.pdf
Consortium for School Networking and FrameWorks Institute. (2012). Making progress: Rethinking state and school district policies concerning mobile technologies and social media. Available: https://splc.org/wp-content/uploads/2018/12/making_progress_2012.pdf
E-Rate Central. (n.d.). Internet safety policies and CIPA: An e-rate primer for schools and libraries. https://e-ratecentral.com/Resources/Educational-Information/CIPA
Foster, J. (2022, January 21). The ultimate online privacy guide (2022). https://web.archive.org/web/20221010120657/https://webhostingprof.com/best-vpns/online-privacy-guide/
Frazier, S. (2022, August 1). Women's guide to cyber safety 2022. https://www.wizcase.com/blog/comprehensive-online-security-guide-for-women/
Guhlin, M. (2005, March 1). Free and low cost software to make computing easier [Online]. TechLearning Magazine. https://www.techlearning.com/news/free-and-low-cost-software-to-make-computing-easier
ILO Group. (2024, March). Framework for implementing artificial intelligence (AI) in K-12 education. https://www.ilogroup.com/wp-content/uploads/2024/03/Framework-for-Implementing-Artificial-Intelligence-AI-in-K-12-Education_v1.0.pdf
Johnson, A. F. (2018, March 12). When can you search a student's phone? THE Journal. https://thejournal.com/articles/2018/03/12/when-can-you-search.aspx
Martinez, S. (2020, February 7). What tech vision are you sharing with students and parents? District Administration. https://districtadministration.com/what-tech-vision-are-you-sharing-with-students-and-families
Michigan Virtual. (2024). Sample guidance on staff use of generative AI for K-12 school districts. https://michiganvirtual.org/resources/ai/resource-bank/k12guidance/
Minow, M. (2002). The Children's Internet Protection Act: The recent district court decision in context, for librarians and library patrons. Law Library Resource Xchange, LLC. https://www.llrx.com/2002/06/features-the-childrens-internet-protection-act-the-recent-district-court-decision-in-context-for-librarians-and-library-pat/
Mishra, G. (2009, May 11). Digital activism & the 4Cs social media framework.Global Voices. https://advox.globalvoices.org/2009/05/11/digital-activism-the-4cs-social-media-framework/
"Mobile Tech Transforms Higher Education: 5 Key Trends to Watch." (2012). https://img.en25.com/Web/LenovoGroup/5_Key_Trends_to_Watch.pdf
Nagel, D. (2021, October 8). K-12 cybersecurity act signed into law. THE Journal. https://thejournal.com/articles/2021/10/08/k12-cybersecurity-act-signed-into-law.aspx
National Conference of State Legislatures. (2022). State internet filtering laws. https://web.archive.org/web/20220423181412/https://www.ncsl.org/research/telecommunications-and-information-technology/state-internet-filtering-laws.aspx
National Institute of Standards and Technology. (2018). Framework for improving critical infrastructure cybersecurity (version 1.1). https://www.nist.gov/cyberframework/framework
Nunez, J., & Elgersma, C. (2024, June 5). A community-first approach to cellphone bans. Common Sense Education. https://www.commonsense.org/education/articles/a-community-first-approach-to-cellphone-bans
Ohio Department of Education and Workforce. (2025). AI model policy for Ohio districts and schools. https://education.ohio.gov/Topics/AI-in-Ohio-s-Education/Model-Policy
Pierce, M. (2012, March 2). Student safety in the age of facebook. THE Journal. https://thejournal.com/Articles/2012/03/02/online-safety.aspx
Privacy Technical Assistance Center. (2014, February 25). Protecting student privacy while using online educational services: Requirements and best practices. Washington, DC: U.S. Department of Education. hthttps://studentprivacy.ed.gov/resources/protecting-student-privacy-while-using-online-educational-services-requirements-and-best
Readiness and Emergency Management for Schools Technical Assistance Center. (n.d.). Cybersecurity for schools fact sheet. https://cdpsdocs.state.co.us/safeschools/Resources/Cybersecurity_K-12_Fact_Sheet_508C.PDF
Reyes, I., Wijesekera, P., Reardon, J., Elazari, A., Razaghpanah, A., Vallina-Rodriguez, N., & Egelman, S. (2018). “Won’t Somebody Think of the Children?” Examining COPPA Compliance at Scale. Proceedings on Privacy Enhancing Technologies, 2018(3), 63–83. https://petsymposium.org/2018/files/papers/issue3/popets-2018-0021.pdf
Robinson, J. (2013, February 21). From the principal's office: Ideas for establishing & revising your school or district's BYOD policies. TL Advisor Blog. https://www.techlearning.com/tl-advisor-blog/5405
Roschelle, J., Fusco, J., & Ruiz, P. (2024, February 26). Review of guidance from seven states on AI in education. Digital Promise. https://files.eric.ed.gov/fulltext/ED671241.pdf
Scrogan, L. (2007, August/September). AUPs in a Web 2.0 world. EdTech magazine. https://edtechmagazine.com/k12/article/2007/07/aups-web-20-world
Stansbury, M. (2017, December 28). 5 technologies to avoid in the classroom - and what to use instead. eSchool News. https://www.eschoolnews.com/2017/12/28/2-technologies-avoid-classroom/
U.S. Department of Education, Office of Educational Technology. (2014). Future ready schools: Building technology infrastructure for learning. Washington, D.C. https://eric.ed.gov/?id=ED589997
U.S. Department of Education, Office of Educational Technology. (2024). Planning together: A playbook for student personal device policies. Washington, D.C. https://files.eric.ed.gov/fulltext/ED670774.pdf
Wallace, A. (2013, October 25). CIPA: 10 years later, there is still confusion. TechLearning Magazine: Features. https://www.techlearning.com/news/cipa-10-years-later-there-is-still-confusion
Wells, J., & Lewis, L. (2006, November). Internet access in U.S. public schools and classrooms: 1994-2005 (NCES 2007020). U.S. Department of Education. Washington, DC: National Center for Education Statistics. https://nces.ed.gov/pubsearch/pubsinfo.asp?pubid=2007020
Willard, N. (2009). A web 2.0 approach to internet safety. Education World. https://www.educationworld.com/a_tech/columnists/willard/willard008.shtml
![]()
![]() See other Technology Integration pages:
See other Technology Integration pages:
Part 2: Technology Integration Resources: Page 1 | 2 | 3 | 4
Part 1: Essential Questions | Part 3: Web Page Design | Part 4: Multimedia in Projects